Anonymous tracing, a dangerous oxymoron
A risk analysis for non-specialists
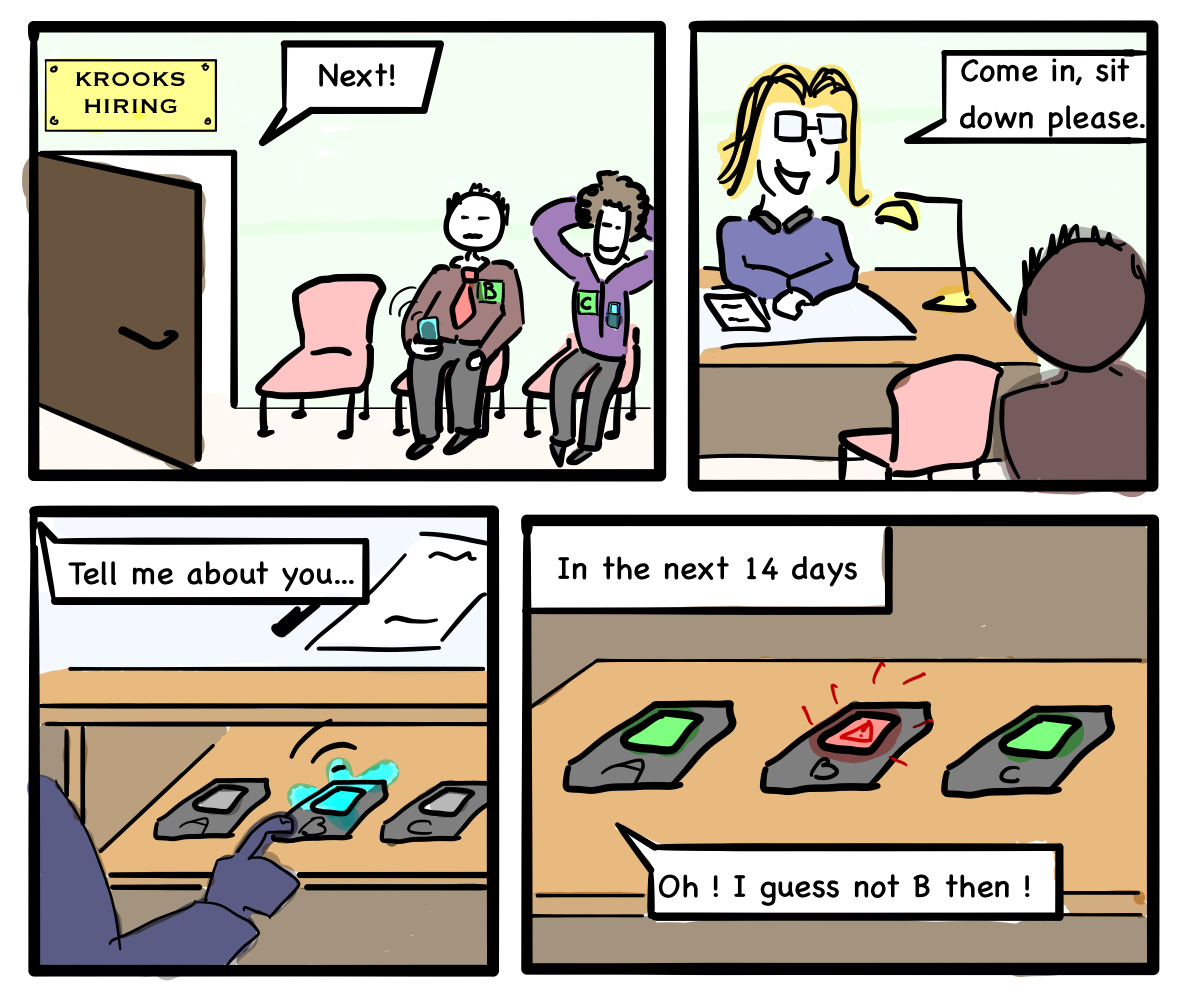
Figure 1: The KROOKS company intends to recruit a temporary employee. They want to make sure that the candidate does not fall sick between the job interview and signing the contract. They therefore use a dedicated phone that is switched on only during the interview, and which will receive an alert if the candidate later tests positive for the disease.
Automated contact tracing using a smartphone application yields many risks that are independent from the specifics of the inner-workings of said application. We are specialists in cryptography, security or technology law. Our expertise lies notably in our ability to anticipate the various abuses, misuses, and other ill-intentioned behaviours that could arise. We offer an analysis of the risks posed by such an application that is based on the study of concrete scenarios, and which is aimed at non-specialists.
Summary :
| There is no patient name database | TRUE |
| The data is anonymous | FALSE |
| It is impossible to figure out who contaminated who | FALSE |
| It is impossible to know if a specific person is ill or not | FALSE |
| It is impossible to trigger a false alarm | FALSE |
| The use of Bluetooth is not a problem from a security standpoint | FALSE |
| This scheme completely prevents large scale snooping | FALSE |
Contact : contact@risques-tracage.fr
In an attempt to arrest the progress of the COVID-19 epidemic, France plans to put in place a system intended to trace patients using a mobile app. The developers of this type of app intend to ensure that they are respectful of privacy. However, this notion remains vague. We hope, therefore, to contribute to the public debate by clarifying what a tracking app could and could not guarantee, with the intention that people can form an opinion on whether its deployment is advisable.
The usefulness of this application lies in its capacity to detect contacts at risk, and to use this information in a relevant manner with other measures to fight the epidemic, such as screening or quarantine. Not having expertise in epidemiology, we are mindful of not judging the impact of the tracking app on the spread of the disease. However, this evaluation would seem indispensable to balance the possible benefits and risks.
Our expertise as specialists in cryptography, security or technology law lies, in particular, in our ability to anticipate the multiple abuses and misappropriations, and other malicious behavior, that could emerge. At present, a lively debate is ongoing on the proposed applications between specialists in the field of security, often pitting so-called "centralised" applications against "decentralised" ones. Regardless of these technical considerations, we intend to alert people to the intrinsic dangers of a tracking application. Using different scenarios such as the one below, we elucidate the possible abuses of such a technology, regardless of the details of its implementation.
Who are we?
- Xavier Bonnetain, University of Waterloo, Canada ;
- Anne Canteaut, Inria ;
- Véronique Cortier, CNRS, Loria ;
- Pierrick Gaudry, CNRS, Loria ;
- Lucca Hirschi, Inria ;
- Steve Kremer, Inria ;
- Stéphanie Lacour, CNRS ;
- Matthieu Lequesne, Sorbonne Université and Inria ;
- Gaëtan Leurent, Inria ;
- Léo Perrin, Inria ;
- André Schrottenloher, Inria ;
- Emmanuel Thomé, Inria ;
- Serge Vaudenay, EPFL, Suisse ;
- Christophe Vuillot, Inria.
Translator
- Tom Lancaster, Durham University.
- We also thank Cally Gatehouse and Caroline Claisse (Northumbria University, UK) for their help with the translation.
Licence and translation
This document is under licence CC BY-SA 4.0. In particular, you are free to translate it to other languages. Should this happen, the authors of the initial document are not liable for these translations.
 French Version
French Version